Nearly million was stolen from approximately 57,000 crypto users by criminals who use phishing scams to lure victims. The Scam Sniffer data highlights that most of the thefts occurred on the Ethereum chain, with ERC-20 tokens being the most targeted. Unlike in January, the number of victims who lost digital funds exceeding million […]
Nearly million was stolen from approximately 57,000 crypto users by criminals who use phishing scams to lure victims. The Scam Sniffer data highlights that most of the thefts occurred on the Ethereum chain, with ERC-20 tokens being the most targeted. Unlike in January, the number of victims who lost digital funds exceeding million […]
Bitcoin News
Peckshield: Cryptocurrency Hackers Stole Over $360 Million in February
 Cryptocurrency hackers stole over 0 million during February, almost doubling the amount stolen in January. According to Peckshield, a cryptocurrency and blockchain security firm, the largest hack event in February involved a security breach in Playdapp, a Web3 gaming platform, that lost 0 million four days after being attacked. Fixedfloat, a cryptocurrency exchange, also lost […]
Cryptocurrency hackers stole over 0 million during February, almost doubling the amount stolen in January. According to Peckshield, a cryptocurrency and blockchain security firm, the largest hack event in February involved a security breach in Playdapp, a Web3 gaming platform, that lost 0 million four days after being attacked. Fixedfloat, a cryptocurrency exchange, also lost […]
Bitcoin News
How One Man Stole $3 Billion in Bitcoin and Got Away for Nearly a Decade

From purchasing cocaine to uncovering a multimillion-dollar glitch, the story of James “Jimmy” Zhong reads like a dark comedy. Zhong, a computer science graduate, exploited a vulnerability on Silk Road to steal over 50,000 bitcoin, evading detection for nearly a decade while living a life of luxury.
The Unbelievable Tale of Jimmy Zhong: From Cocaine Purchase to Bitcoin Billionaire
This is a tale tailor made for the Coen brothers, ala “Fargo” or “Burn After Reading.” James “Jimmy” Zhong, a 28-year-old University of Georgia computer science graduate, executed the largest bitcoin theft in history. From the infamous dark web market Silk Road, Zhong pilfered over 50,000 bitcoin, valued at approximately .4 billion in 2023. Recently, a poster on X that goes by the pseudonym BTCGandalf, recounted Jimmy’s story with colorful details. Read the thread for a story-like recounting with many more details than this brief summary.
The Incredible Story of the Unlikely Man Who Stole 50,000 BTC (B) From the Silk Road
🧵 pic.twitter.com/mSwSPZPcPE— GANDALF (@BTCGandalf) January 26, 2024
Between 2012 and 2014, exploiting a flaw on the Silk Road, Zhong was able to drain the site’s hot wallet of its massive bitcoin stash, over 51,680 bitcoin. In one of those stranger-than-fiction moments, Zhong later confessed to discovering and exploiting the glitch on Silk Road after purchasing cocaine.
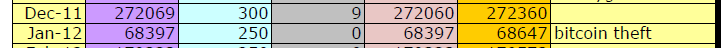
Vinny D’Agostino, the FBI trial agent for the original Silk Road Case, said in a reply post to the thread that Ross Ulbricht, founder of Silk Road, “knew his security skills were weak and wanted to close any gaps. The loss of the 50,000 bitcoin was major.” D’Agostino provided an image of a spreadsheet Ross kept to log, among other things, his net worth. “The orange [is] his net worth, which took a big hit. All of this evidence was found on his Samsung 700z laptop which he was using at the time of arrest.”
Despite his lavish spending and previous run-ins with the law, including a DUI and a felony drug possession charge, Zhong remained undetected for almost a decade. However, his luck ran out when two things happened in 2019.
First, in March 2019 someone broke into his house stealing approximately 0,000 in cash and bitcoin. Inexplicably, Zhong called 911, asking the police to carry out an investigation. Second, around this time Zhong had made the mistake of transferring a small portion of his stolen bitcoin to a KYC-compliant exchange, catching the IRS’s attention.
The subsequent investigation by IRS agents, collaborating with local Athens police, who had previously believed Zhong’s story of being a savvy bitcoin investor, launched a covert operation to unravel the truth. This culminated in a search of Zhong’s property in November 2019, which unveiled the majority of the stolen Silk Road bitcoin hidden in a popcorn tin.
Zhong was arrested, pleaded guilty to one count of wire fraud, and in 2022 was sentenced to 366 days in prison. His lawyer was able to successfully argue it was a victimless crime, as he stole from a criminal enterprise.
The rise and fall of James “Jimmy” Zhong was a comedy of errors. Or, as D’Agostino puts it,
“[T]he fact that Jimmy called the cops after having some of his bitcoin stolen highlights how many cyber criminals (including Ross) were brilliant but lacked street smarts.”
Do you think that Jimmy has some extra bitcoin squirreled away somewhere? Share your thoughts and opinions about this subject in the comments section below.
North Korea-Affiliated Hackers Stole $600 Million in 2023 — Ten Times More Damaging Than Anyone Else

North Korea-affiliated hackers stole digital assets worth 0 million in the past year. According to a TRM Labs report, this figure will likely rise to 0 million if additional attacks which occurred at the tail end of the year are traced to the same hackers. North Korea and its affiliates reportedly now possess a hacking prowess which requires ongoing “vigilance and innovation from business and governments.”
DPRK Hacks Ten Times More Damaging
According to the latest research by the blockchain intelligence firm TRM Labs, North Korea-affiliated hackers stole digital assets worth at least 0 million in 2023. If additional hacks that occurred in the final days of that year are confirmed as North Korean attacks, this figure is likely to rise to 0 million.
TRM Labs’ new report on suspected North Korean hacks acknowledges that the value of digital assets stolen in the past year is 30% lower than the 0 million siphoned in 2022. However, the intelligence firm’s findings suggest that hacks orchestrated by the Democratic People’s Republic of Korea (DPRK) “were on average ten times as damaging as those not linked to North Korea.”
As previously reported by Bitcoin.com News, North Korea, which is under United Nations (UN) sanctions, is accused of using stolen digital assets to fund its suspected nuclear weapons program. Some observers believe that North Korea’s ability to fund its programs using stolen digital assets is helping the country undermine UN sanctions.
Stolen Digital Assets Mostly Swapped With USDT or Tron
Explaining the North Korea-affiliated hackers’ modus operandi, the TRM Labs report said:
“North Korea conducts nearly all of its attacks by compromising private keys and seed phrases, which are critical security elements of digital wallets. Hackers transfer the victims’ digital assets to wallet addresses controlled by North Korean operatives. They are then swapped mostly for USDT or Tron and converted to hard currency using high-volume OTC brokers.”
Meanwhile, the report also highlighted how the DPRK has continued to launder stolen crypto funds even after U.S. authorities have sanctioned the country’s previous go-to crypto mixers. The report ends by acknowledging that North Korea and its affiliates now possess a hacking prowess which requires ongoing “vigilance and innovation from business and governments.”
What are your thoughts on this story? Let us know what you think in the comments section below.
Prosecutor: FTX Boss Sam Bankman-Fried Stole Billions From Customers, Lied About It

Federal prosecutor Nicolas Roos argued this week that Sam Bankman-Fried stole billions in customer funds from his cryptocurrency exchange FTX and lied repeatedly to cover it up, actions that make him guilty on all counts. The prosecutor’s closing argument paints a picture of Bankman-Fried building a mountain of lies that eventually collapsed, “leaving countless victims in its wake.”
From Crypto King to the Courtroom’s Closing Arguments: The Bankman-Fried Saga
Almost a year ago, customers began trying to withdraw funds from FTX, but their requests went unprocessed as FTX went bankrupt with billion missing, prosecutor Roos told the court on Novemeber 1, 2023. The federal government’s closing argument was published by Matthew Russell Lee from the Inner City Press.
Roos argued that Sam Bankman-Fried spent FTX customer money to cover expenses, buy property and make political donations in a “pyramid of deceit” that eventually collapsed. Roos said Bankman-Fried knew taking the money was wrong but believed he could evade consequences.
“He thought he was smarter, and could walk his way out of it. Today, with you, that ends,” Roos said to the jurors.
Roos said Bankman-Fried set up a secret system allowing his quantitive trading firm Alameda Research to take FTX customer funds with zero risk of liquidation. Roos called this stealing: “[It’s] fraud. It’s stealing plain and simple.” Roos said Bankman-Fried lied repeatedly on the stand, unable to recall details from his own business. “Over three days he took the stand and he lied. You’d have to ignore all the evidence,” Roos said.
The federal prosecutor also recounted how Bankman-Fried failed to remember his statements or decisions, saying:
He couldn’t remember a single detail. It was uncomfortable. 140 times…
Roos outlined how Bankman-Fried allegedly used FTX customer money to buy back FTX stock and acquire luxury property despite subordinates warning him it was unwise. Roos said Bankman-Fried omitted negative information from balance sheets sent to investors and lenders, calling it fraud. The U.S. attorney added:
He took the money and played roulette with it. He was stealing.
Roos completely rejected Bankman-Fried’s good faith defense, citing deleted communications and testimony he acknowledged issues but proceeded anyway. Roos called margin lending explanations false excuses, saying customers had to opt into margin programs separately. In conclusion, Roos said: “Let the evidence prevail over his storytelling. He lied. He is guilty. Reach that verdict: that he is guilty.”
What do you think about the federal prosecutor’s closing arguments against Sam Bankman-Fried? Share your thoughts and opinions about this subject in the comments section below.
Report: North Korea Affiliated Cybercriminals Stole $721 Milion Worth Crypto Assets From Japan

Between 2017 and 2022, hacking groups affiliated with North Korea are thought to have stolen crypto assets worth 1 million from Japan alone. According to the findings of a study by Elliptic, hackers were primarily focused on Japan and Vietnam because operators from the two countries had lax security systems.
Japan Losses Equivalent to 30% of the Global Total
According to the findings of a study conducted by the blockchain intelligence firm Elliptic, North Korea coordinated cyber attacks targeting Japanese crypto assets netted 1 million worth of digital assets between 2022 and 2017. This figure is equivalent to 30% of total global losses that have been attributed to North Korea-affiliated hacker groups.
As per the report in Nikkei Asia, which commissioned the study, the value of crypto assets stolen from Japan alone is 8.8 times more than North Korea’s 2021 export figure. While the cyber attackers are thought to have targeted several countries, the Nikkei report suggested that Japan and Vietnam were especially targeted because of their rapidly growing crypto markets.
Hackers are also thought to have zeroed in on the two countries because operators there used lax security systems. One of the targeted operators or crypto exchange platforms, Zaif, which lost .4 million (7 billion yen) in 2018, has since shut down.
Crypto Exchanges Primary Targets
North Korea, which is under U.S. and United Nations sanctions, has struggled to secure the foreign currency that it needs. To compensate for this, hacker groups affiliated with Pyongyang including the Lazarus Group have been handed the task of stealing crypto assets for North Korea. To achieve this, the hacker groups have used two types of cyber attacks; hacking and ransomware.
However, according to the report, North Korea-affiliated cybercriminals have primarily used hacking because these methods enable Pyongyang to “bring in a huge haul of crypto assets” from just one targeted crypto exchange. The hacking also enables North Korea, which is reeling from the effects of sanctions, to raise foreign currency.
Besides Japan, the same hacker groups are said to have targeted the United States and other Asia countries like Hong Kong. As noted in the report, the hacker groups are believed to have stolen 7 million from the United States and 1 million from Hong Kong.
What are your thoughts on this story? Let us know what you think in the comments section below.
This Is How A Hacker Stole Roughly $200 Million From Euler Finance, A DeFi Protocol
Euler Finance, a decentralized finance (DeFi) lending protocol on Ethereum, has lost approximately 0 million through a flash loan hack. This loss makes it the biggest DeFi hack in 2023.
Euler Finance’s 0 Million Exploit
On Mar. 13, 2023, Euler Finance confirmed that it had suffered an attack, resulting in approximately a 0 million loss. The protocol is now working with law enforcement and security professionals.
We are aware and our team is currently working with security professionals and law enforcement. We will release further information as soon as we have it. https://t.co/bjm6xyYcxf
— Euler Labs (@eulerfinance) March 13, 2023
To execute the hack, the attacker targeted four tokens: DAI, an algorithmic stablecoin; wrapped-Bitcoin (WBTC); staked-Ethereum (sETH); and USDC, a fiat-backed stablecoin. In recent months, Euler Finance has become popular for offering liquid staking derivatives (LSD) services. Notably, it comes ahead of the Shanghai-Capella upgrade on Ethereum, a smart contract platform.
According to Dedaub, a smart contract auditing service provider, the attacker used flash loans from Aave, a non-custodial lending protocol, to carry out the attack. Ahead of this, funds were first bridged from BNB Smart Chain (BSC) before it was deployed to break Euler Finance.
In a flash loan attack, the attacker borrows a large token amount without collateral, typically using a flash loan. Afterward, they use that loan to manipulate other tokens’ value in a pool, in most cases driving down the price of the target asset. With this, they can buy that token at a lower price and quickly sell it back for a profit once the price recovers.
The Flash Loan Attack
In Euler Finance’s case, the flash loan was leveraged in two instances forcing massive liquidations. Specifically, the attacker tricked the protocol into falsely assuming it held a low amount of eToken, a collateral token issued by Euler based on whichever token is deposited on the protocol.
They then borrowed 10x the deposited amount from Euler, receiving 195.6 million eDAI and 200 million dDAI.
Euler suffered an attack
Analyzing 1 tx that shows an .9m+ return for the attacker
1. Flash loan2. Deposit 20m DAI3. Mint 200m eDAI4. Repay 10m DAI5. Mint 200m eDAI6. Donate 100m eDAI to reserves7. Liquidate yourself for 259m eDAI yields 38.9m DAI8. Close flashloan pic.twitter.com/8cjHwDgX3y
— Dedaub (@dedaub) March 13, 2023
This type of exploit is known as a liquidity attack. It’s also one of the most common types of DeFi hacks.
Essentially, attackers manipulate the protocol’s liquidity calculations, which allows the attacker to borrow more funds than they should be able to, leading to massive losses for the protocol and its users.
The Euler hack is the latest in many DeFi exploits that have plagued the industry recently. According to blockchain analytics firm Chainalysis, over billion was stolen from DeFi protocols via hacks or exploits in 2022 alone.
2/ At this rate, 2022 will likely surpass 2021 as the biggest year for hacking on record. So far, hackers have grossed over billion dollars across 125 hacks. pic.twitter.com/vgT3pz2iOu
— Chainalysis (@chainalysis) October 12, 2022
DeFiLlama data shows hackers stole over million in February 2023. Among those targeted include Orion, dForce network, and Platypus Finance.
In February, the dForce network lost .65 million, while Platypus Finance was hacked for over million.
North Korea Stole Record Amount of Crypto Assets in 2022, UN Report Unveils

The regime in North Korea has managed to steal more cryptocurrency last year than in previous years, according to a draft U.N. report. Despite the difference between quoted estimates, the authors conclude that 2022 was a record-breaking year for crypto theft, to be blamed on the hermit state.
Cybercrime Groups Linked to North Korea Get Hold of Crypto Worth Over Billion in a Year
North Korea has stolen more crypto assets in 2022 than in any other year, according to a United Nations report which is to be released by the end of this month or in early March. The draft paper, seen by Reuters and Nikkei Asia, reveals how the isolated country is raising funds through cyberattacks and in circumvention of international restrictions.
The document, which is still confidential at this point in time, was submitted to the U.N. Security Council’s committee on North Korea sanctions on Friday. The findings in it are based on information provided by U.N. member states and cybersecurity firms.
Its authors quote different estimates. One produced by South Korea suggests that hackers controlled by Pyongyang acquired crypto worth 0 million during the studied period, while a cybersecurity company has assessed that the virtual money they obtained exceeded billion. In any case, the independent sanctions monitors believe that:
A higher value of cryptocurrency assets was stolen by DPRK actors in 2022 than in any previous year.
Tenth of Total Stolen From South Korean Accounts
The variation in U.S.-dollar equivalent of cryptocurrency in recent months is likely to have affected these estimates, the report noted while highlighting that both estimates indicated that 2022 was a record-breaking year for crypto theft associated with the Democratic People’s Republic of Korea (DPRK).
A similar conclusion stems from data compiled by Chainalysis. Last week, the U.S.-headquartered blockchain forensics firm said that North Korea-linked hackers, such as the members of the Lazarus Group, have been particularly active last year, having stolen around .7 billion worth of coins.
Quoting intelligence authorities, the Seoul-based Chosun Ilbo daily wrote on Tuesday that about 10% of the total has been extracted from accounts of South Korean companies and individuals. It also remarked that the money is believed to have been laundered and used to finance the North’s nuclear and missile development programs.
The sanctions monitors said that the majority of cyberattacks were conducted by hacking teams controlled by the DPRK’s Reconnaissance General Bureau, the communist state’s main intelligence agency. Besides Lazarus, these also include groups like Kimsuky and Andariel. The U.N. report also noted that the techniques they are employing are becoming more sophisticated which hampers tracking.
Do you think North Korea-linked actors will steal even more cryptocurrency in 2023? Share your thoughts on the subject in the comments section below.
Hackers Stole $3.8 Billion From Crypto Firms in 2022, Says Chainalysis

Blockchain analytics firm Chainalysis says 2022 was “the biggest year ever for crypto hacking,” with .8 billion stolen from cryptocurrency businesses. The firm added that decentralized finance (defi) protocol hacks accounted for 82.1% of all cryptocurrency stolen by hackers during the year.
Crypto Hacking Hit Record High in 2022
Blockchain analytics firm Chainalysis published a section of its upcoming 2023 Crypto Crime Report on Wednesday, stating:
2022 was the biggest year ever for crypto hacking, with .8 billion stolen from cryptocurrency businesses.
The firm explained that crypto hacking activity significantly increased in March and peaked in October — the month which “became the biggest single month ever for cryptocurrency hacking, as 5.7 million was stolen in 32 separate attacks,” Chainalysis described.
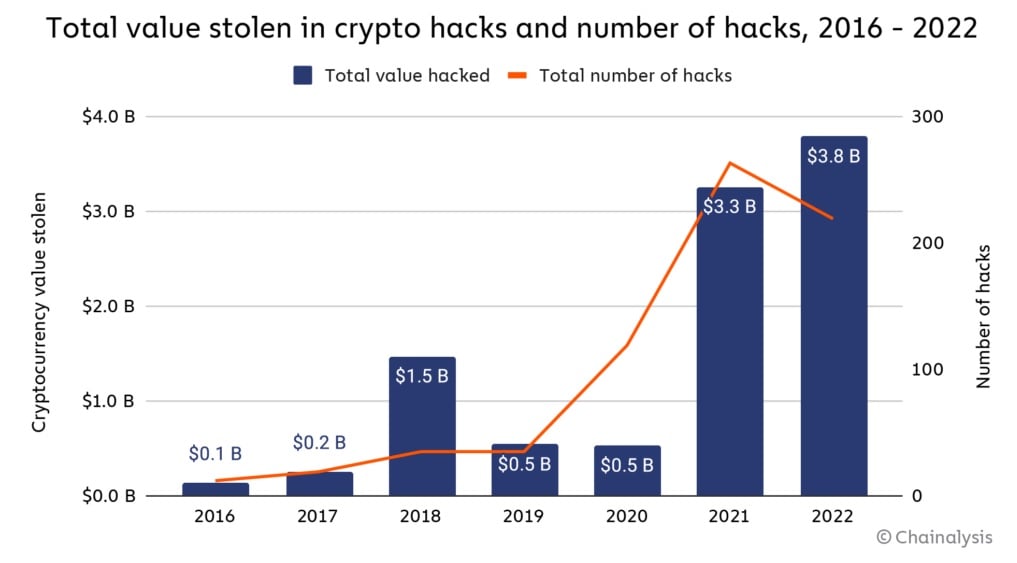
The firm added that “82.1% of all cryptocurrency stolen by hackers — a total of .1 billion” came from decentralized finance (defi) hacks. Noting that this percentage was up from 73.3% in 2021, the firm pointed out that .1 billion of 64% came from cross-chain bridge protocols specifically.
Chainalysis also detailed that “North Korea-linked hackers … have been by far the most prolific cryptocurrency hackers over the last few years,” elaborating:
In 2022, they shattered their own records for theft, stealing an estimated .7 billion worth of cryptocurrency across several hacks we’ve attributed to them.
Moreover, the blockchain analytics firm stated that North Korea-linked hackers stole .1 billion of that amount from defi protocols, making North Korea “one of the driving forces behind the defi hacking trend that intensified in 2022.” Besides defi protocols, Chainalysis noted that “North Korea-linked hackers also tend to send large sums to mixers, which have typically been the cornerstone of their money laundering process.”
The firm further detailed that “For much of 2021 and 2022, North Korea-linked hackers almost exclusively used Tornado Cash to launder cryptocurrency stolen in hacks.” Ethereum mixer Tornado Cash was sanctioned by the U.S. government in August last year.
What do you think about hackers stealing .8 billion from cryptocurrency firms last year? Let us know in the comments section below.
Coinbase CEO Brian Armstrong Allegedly Stole Startup’s Work, New Lawsuit Reveals
A blockchain firm has sued Coinbase CEO Brian Armstrong, alleging that he stole their technology while passing it off as an investment.
Stolen Work Passed Off As Investment?
According to a lawsuit alleging that Coinbase committed fraud, its CEO took the work of a blockchain firm for a competitor project under the premise of a potential investment.
The lawsuit was filed on Friday in California by MouseBelt Labs, a blockchain accelerator, Coinbase CEO Brian Armstrong was designing a platform for publishing academic research that used tradable tokens when he learned of a similar platform called Knowledgr. According to the lawsuit, Armstrong’s ResearchHub, like Knowledgr, would reward participants with tokens akin to bitcoin.
Patrick Joyce worked on Knowledgr with MouseBelt’s technical and financial assistance. The accelerator had begun communicating with Joyce in 2018, but the two only signed all of the necessary agreements in May 2019 to begin working together.
At first, everything seemed to be going to plan. Joyce was on track to fulfill agreed objectives, and MouseBelt was staying on track to satisfy its contractual obligations.
In Armstrong’s article, “Ideas for Improving Scientific Research,” was published, he encouraged anyone interested in sharing ideas to contact him. Patrick Joyce was one of those who did.
Knowledgr drew Armstrong’s attention, and he provided a cash commitment as well as the opportunity to launch the tokens on Coinbase. Knowledgr agreed.
Armstrong, according to MouseBelt, didn’t want to assist to fund and grow Knowledgr, but rather take the latter’s idea and kill a competitor. In essence, MouseBelt claims that Coinbase plagiarized Knowledgr’s innovations and incorporated them into its own platform. According to the suit,
“It was the intention of Armstrong and the other defendants to steal MouseBelt’s work for themselves, not only to eliminate a potential competitor, but to secure for ResearchHub the benefits of the financial, design and technical resources that MouseBelt has. put into Knowledgr, allowing ResearchHub to launch earlier and more cheaply a successful platform based entirely or largely on the work of MouseBelt.”
Coinbase Currently trading at 8. Source: TradingView
Related article | Brian Armstrong Says China’s Digital Currency Is A Threat To U.S.
Armstrong Accused Of Playing A Power Game
Although Knowledgr was still in its early phases of development at the time, and Armstrong’s project was simply a concept, one thing is certain: ResearchHub is now up and running, whereas Knowledgr is not.
The lawsuit has elicited no public response from Coinbase. It remains to be seen how valid the lawsuit’s grounds are, and the exchange is expected to retaliate vehemently. Despite the fact that the exchange has been the subject of various scandals in the past, it has continued to develop.
Accusations of racism and a “company first” policy in the workplace have been two of Coinbase’s biggest controversies in the past. Some have criticized the latter for prohibiting difficult debates in the workplace, claiming that it was not in the spirit of decentralization.
Armstrong was also sued by the Securities and Exchange Commission (SEC) in September for a program that allows crypto investors to earn interest on their investments.
The lawsuit forced Armstrong to clarify the situation, according to The Washington Post. He revealed that the SEC classed Coinbase’s product as a sort of security that must be registered with the US government in a lengthy, 21-part Twitter conversation.
Related article | Coinbase IPO Will See Co-Founder Brian Armstrong Join The Ultra Rich
Featured Image From TechCrunch, Chart by TradingView
NewsBTC