 A new report by blockchain intelligence firm TRM reveals that crypto thefts in the first half of 2024 have doubled compared to 2023, with .38 billion stolen by June 24. Major hacks constitute 70% of losses, with private key compromises and smart contract exploits as top attack vectors. Crypto projects are advised to adopt comprehensive […]
A new report by blockchain intelligence firm TRM reveals that crypto thefts in the first half of 2024 have doubled compared to 2023, with .38 billion stolen by June 24. Major hacks constitute 70% of losses, with private key compromises and smart contract exploits as top attack vectors. Crypto projects are advised to adopt comprehensive […]
Bitcoin News
Vietnamese Hackers Indicted in US for $71M Cybercrime Involving Cryptocurrency
 Four Vietnamese nationals were charged in a U.S. court for a series of cyber intrusions causing over million in losses. The defendants, part of the cybercrime group “FIN9,” allegedly hacked U.S. companies from May 2018 to October 2021, stealing non-public information, employee benefits, and funds. They used stolen personal and credit card information to […]
Four Vietnamese nationals were charged in a U.S. court for a series of cyber intrusions causing over million in losses. The defendants, part of the cybercrime group “FIN9,” allegedly hacked U.S. companies from May 2018 to October 2021, stealing non-public information, employee benefits, and funds. They used stolen personal and credit card information to […]
Bitcoin News
Lost And Found: Hackers Successfully Access Decade-Old Bitcoin Wallet, Retrieve $3 Million
In an extraordinary turn of events, two hackers have successfully cracked the long-forgotten password of a digital wallet, leading to the recovery of approximately million worth of Bitcoin (BTC).
Lost Bitcoin Fortune Unlocked
As reported by Wired, the story began in 2013 when an individual known by the alias “Michael” securely stored his Bitcoin holdings in a password-protected digital wallet. Unfortunately, over time, he lost access to the wallet due to a corrupted file containing the 20-character password generated using the RoboForm password manager.
Despite his efforts to prioritize security, Michael’s concerns about potential hacking led him to refrain from storing the password in his manager, inadvertently locking himself out of his fortune.
Enter Joe Grand, a renowned electrical engineer and hardware hacker, popularly known as “Kingpin.” In 2022, Grand gained recognition for aiding another cryptocurrency wallet owner in recovering million worth of digital assets after forgetting the PIN to his Trezor wallet. Since then, numerous individuals have approached Grand seeking his expertise, but he selectively chooses his projects.
Michael initially approached Grand two years ago, seeking assistance in recovering his lost Bitcoin. However, due to the unique challenges posed by a software-based wallet, Grand declined the request.
Nonetheless, Michael persisted, and last June, Grand agreed to give it another shot, teaming up with a fellow hacker named Bruno from Germany.
Months of reverse engineering led Grand and Bruno to a significant breakthrough. They discovered a flaw in the pseudo-random number generator used by the RoboForm program, which was employed by Michael in 2013.
The flaw tied the generated passwords to the date and time on the user’s computer, making them predictable. Armed with this knowledge, the hackers devised a plan to exploit the flaw and crack the password.
The major hurdle in this process was Michael’s inability to recall the exact date when the password was generated. However, armed with the knowledge that Bitcoin had been moved into the wallet for the first time on April 14, 2013, Grand and Bruno configured RoboForm to generate passwords within a specific time frame, utilizing the parameters used by Michael.
From Forgotten To Found
Despite initial failed attempts, Grand and Bruno persisted, adjusting the time frame and parameters until they finally struck gold. On November 15, 2023, they discovered the correct password—20 characters long and generated on May 15, 2013. The long-lost Bitcoin treasure was finally within Michael’s grasp.
However, the report notes that the successful recovery of Michael’s assets raises concerns about password security, particularly for users who generated passwords using earlier versions of RoboForm.
While Siber Systems, the company behind RoboForm, claims to have fixed the flaw in 2015, questions remain about the vulnerability of older passwords. Grand stresses the importance of understanding the improvements made to password generation in newer versions.
Having access to his Bitcoin once again, Michael experienced a stroke of luck. He waited for the value of Bitcoin to rise before selling a portion of his newfound fortune. With 30 BTC currently valued at million, Michael eagerly anticipates the potential for even greater returns as he aims for a future surge to 0,000 per coin.
As of press time, the largest cryptocurrency on the market is trading at ,200, consolidating for the past week below the key ,000 threshold that is crucial to BTC’s uptrend prospects.
Featured image from Shutterstock, chart from TradingView.com
Defi Protocol Sonne Finance Reports Major Security Breach, $20 Million Lost to Hackers
 Sonne Finance, a decentralized liquidity market protocol, was hit by a cyberattack, with initial losses of million in USD Coin and Wrapped Ethereum from its Optimism chain quickly escalating to million, as detected by blockchain security firm Cyvers on May 15. Following the attack, Sonne Finance suspended its Optimism Market and assured that […]
Sonne Finance, a decentralized liquidity market protocol, was hit by a cyberattack, with initial losses of million in USD Coin and Wrapped Ethereum from its Optimism chain quickly escalating to million, as detected by blockchain security firm Cyvers on May 15. Following the attack, Sonne Finance suspended its Optimism Market and assured that […]
Bitcoin News
Peckshield: Cryptocurrency Hackers Stole Over $360 Million in February
 Cryptocurrency hackers stole over 0 million during February, almost doubling the amount stolen in January. According to Peckshield, a cryptocurrency and blockchain security firm, the largest hack event in February involved a security breach in Playdapp, a Web3 gaming platform, that lost 0 million four days after being attacked. Fixedfloat, a cryptocurrency exchange, also lost […]
Cryptocurrency hackers stole over 0 million during February, almost doubling the amount stolen in January. According to Peckshield, a cryptocurrency and blockchain security firm, the largest hack event in February involved a security breach in Playdapp, a Web3 gaming platform, that lost 0 million four days after being attacked. Fixedfloat, a cryptocurrency exchange, also lost […]
Bitcoin News
North Korea-Affiliated Hackers Stole $600 Million in 2023 — Ten Times More Damaging Than Anyone Else

North Korea-affiliated hackers stole digital assets worth 0 million in the past year. According to a TRM Labs report, this figure will likely rise to 0 million if additional attacks which occurred at the tail end of the year are traced to the same hackers. North Korea and its affiliates reportedly now possess a hacking prowess which requires ongoing “vigilance and innovation from business and governments.”
DPRK Hacks Ten Times More Damaging
According to the latest research by the blockchain intelligence firm TRM Labs, North Korea-affiliated hackers stole digital assets worth at least 0 million in 2023. If additional hacks that occurred in the final days of that year are confirmed as North Korean attacks, this figure is likely to rise to 0 million.
TRM Labs’ new report on suspected North Korean hacks acknowledges that the value of digital assets stolen in the past year is 30% lower than the 0 million siphoned in 2022. However, the intelligence firm’s findings suggest that hacks orchestrated by the Democratic People’s Republic of Korea (DPRK) “were on average ten times as damaging as those not linked to North Korea.”
As previously reported by Bitcoin.com News, North Korea, which is under United Nations (UN) sanctions, is accused of using stolen digital assets to fund its suspected nuclear weapons program. Some observers believe that North Korea’s ability to fund its programs using stolen digital assets is helping the country undermine UN sanctions.
Stolen Digital Assets Mostly Swapped With USDT or Tron
Explaining the North Korea-affiliated hackers’ modus operandi, the TRM Labs report said:
“North Korea conducts nearly all of its attacks by compromising private keys and seed phrases, which are critical security elements of digital wallets. Hackers transfer the victims’ digital assets to wallet addresses controlled by North Korean operatives. They are then swapped mostly for USDT or Tron and converted to hard currency using high-volume OTC brokers.”
Meanwhile, the report also highlighted how the DPRK has continued to launder stolen crypto funds even after U.S. authorities have sanctioned the country’s previous go-to crypto mixers. The report ends by acknowledging that North Korea and its affiliates now possess a hacking prowess which requires ongoing “vigilance and innovation from business and governments.”
What are your thoughts on this story? Let us know what you think in the comments section below.
OKX DEX Loses Over $400,000 To Hackers – What Happens To Customer Funds?
According to blockchain security company SlowMist, OKX DEX, a decentralized exchange aggregator platform, lost cryptocurrency valued at over 0,000.
An attacker was able to transfer tokens that users had not allowed by compromising the management privileges of a market maker contract, according to the explanation for the vulnerability.
On the OKX DEX aggregator platform, a deprecated proxy contract was the subject of a recent vulnerability that allowed a hacker to obtain administration access to the contract without authorization.
OKX DEX: Deprecated Contract Raises Concerns
When a protocol stops actively using a contract to carry out user transactions, it is considered deprecated. It appears that OKX has updated the contract but hasn’t entirely stopped using it.
SlowMist Security Alert: OKX DEX Proxy Admin Owner’s Private Key Suspected to be Leaked
According to information from SlowMist Zone, the OKX DEX contract appears to have encountered an issue. After SlowMist’s analysis, it was found that when users exchange, they authorize…
— SlowMist (@SlowMist_Team) December 13, 2023
The claimTokens function of the OKX DEX smart contract experienced a problem, according to blockchain security firm SlowMist. The TokenApprove contract, which required user authorization, invokes the ability to send cash to a trustworthy DEX Proxy.
On December 12, the SlowMist team reported that the OKX DEX Proxy Admin Owner upgraded the DEX Proxy contract with a new implementation. The purpose of this new implementation was to invoke the claimTokens function straight from the DEX contract.
The exchange said that 18 of the approved addresses for the contract had been compromised, and linked the event to the management rights of a cancelled OKX DEX market maker contract being compromised.
Additionally, the exchange pledged to pay back all impacted users. It would also carry out a comprehensive security examination in order to stop something similar from happening again.
We regret to inform you that a deprecated smart contract on OKX Dex has been compromised. We have taken immediate action to secure all user funds and revoke the contract permissions. We are working with relevant agencies to locate the stolen funds and will reimburse affected… pic.twitter.com/zDIjhb3ETz
— OKX Web3 (Wallet | DeFi | NFT) (@okxweb3) December 13, 2023
OKX Hack: Actual Damages Unknown
According to PeckShield, another researcher specializing in blockchain security, this vulnerability has cost over .76 million.
In the last 30 days, OKX DEX is thought to have had over 50,000 active user wallets; however, it is unknown how many users were impacted by the most recent hack.
Users should employ caution while communicating with DeFi protocols, especially those supported by well-known firms in the industry, as highlighted by the OKX DEX breach.
Featured image from Shutterstock
Rewarding Hackers With Bug Bounties ‘Inherently Creates a Moral Hazard’ Says Expert

Rewarding hackers who agree to return a portion of the stolen funds not only “creates a moral hazard” but potentially “leads to more security breaches,” a Web3 expert has argued. The recent attacks on Kronos and Kyberswap, as well as the subsequent attempts to engage the hackers, are said to demonstrate why victims of attacks should not rely on appeasing the exploiters.
Effectiveness and Importance of Code Audit
According to the latest Immunefi crypto losses report, cybercriminals successfully siphoned over .7 billion from decentralized and centralized digital asset exchange platforms in the first eleven months of 2023. The thefts have been carried out via hacking, phishing attacks, and outright fraud.
Such attacks have increased in their frequency and boldness over the past few months, leading many, including proponents of decentralized platforms, to question the effectiveness of code audits or how users’ funds are secured. Still, others like Davinder Singh, the CTO at the crypto platform Rocketx, concur with those who argue against rewarding hackers. According to Singh, rewarding hackers who agree to return a portion of the stolen funds “inherently creates a moral hazard.”
Although they are intended to help decentralized finance (defi) platforms improve their security and protect users from malicious attacks, Singh told Bitcoin.com News that offering such rewards “inadvertently incentivizes malicious actors and potentially leads to more security breaches.”
The recent attacks on Kronos and Kyberswap, as well as the subsequent attempts to engage the hackers, potentially demonstrate why exchange platforms should not rely solely on appeasing them. For instance, the malicious actor behind the Kyberswap exploit recently made several seemingly outrageous requests, including demanding full control over Kyber.
As reported by Bitcoin.com News, the hacker is seeking a more favorable arrangement than the Kyberswap team’s offer. This example could lend to the argument that defi platforms should be more focused on finding ways to prevent the attacks.
Tracking Hackers
However, Fraser Edwards, the CEO of the privacy-preserving payment network, Cheqd, told Bitcoin.com News that besides helping platforms recover some of the funds, the offer to reward hackers also helps exchange platforms identify perpetrators of the attacks.
“The offer and any response creates the chance of getting more information on the hacker which could give them away. E.g. do they communicate via specific channels or using usernames which could lead to a real identity? A good example here is how Ross Ulbricht of Silk Road was identified through his username/handle being linked across multiple forums, eventually to his real identity,” Edwards explained.
Meanwhile, Nikolay Angelov, Blockchain Head at crypto lender Nexo, insists that while bug bounties are useful in helping decentralized exchange platforms recover stolen funds, they also help cleanse the hackers’ money. Additionally, in some of the known high-profile cases in which hackers have agreed to return the stolen funds, the sum ultimately recovered has been less than 90%.
Declining User Confidence
When hackers can easily get away with stealing millions of dollars, this inevitably erodes confidence in digital asset platforms. To restore trust, Angelov said platforms must utilize “real-time software code inspections to prevent vulnerabilities.”
While the so-called white hat hackers may be motivated by the challenge or reward, state-backed hackers, on the other hand, have no desire to return the funds. Therefore, bug bounties may not be an effective way of attempting to recover funds. According to Angelov, operators who are at the receiving end of attacks orchestrated by state-backed actors such as the North Korean-affiliated Lazarus Group should “actively seek cooperation with government agencies to prevent stolen funds from entering their platforms.”
Singh, who shares similar sentiments, urged defi players to collaborate by sharing threat intelligence and adopting advanced defence strategies. He added:
“This collective effort is essential to safeguarding the decentralized financial ecosystem against sophisticated state-sponsored threats.”
What are your thoughts on this story? Let us know what you think in the comments section below.
Crypto Mixer Sinbad Sanctioned by OFAC Over Alleged Ties to North Korean Hackers
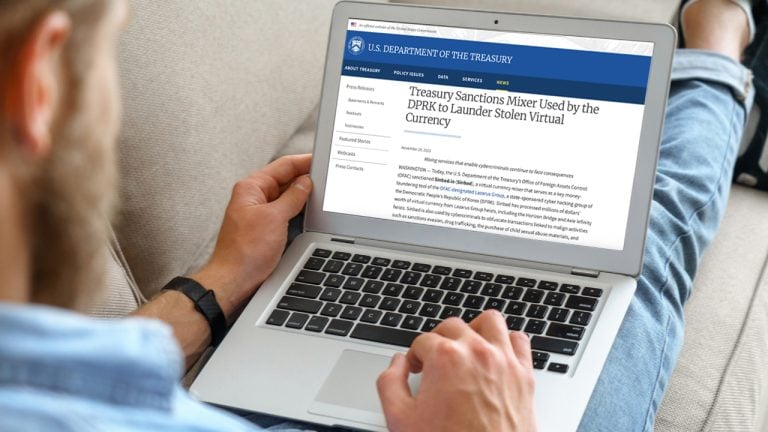
The U.S. Department of the Treasury’s Office of Foreign Assets Control (OFAC) has imposed sanctions on yet another cryptocurrency mixing platform, labeling Sinbad.io as a “key money-laundering tool” used by the North Korean Lazarus Group crime syndicate. Sinbad.io, in addition to handling transactions originating from the Democratic People’s Republic of Korea (DPRK), has also been linked to processing transactions associated with drug trafficking and sales on darknet marketplaces.
OFAC Sanctions Sinbad.io; Agency Claims Mixer Helped Obscure Funds Stolen From Harmony Bridge, Axie, and Atomic Wallet
The U.S. Treasury’s Financial Crimes Enforcement Network (FinCEN) and OFAC have turned their attention towards digital currency mixing protocols. While Tornado Cash and Blender.io were previously targeted by both agencies, the latest subject of scrutiny is the mixer known as Sinbad.io. This service operates as a bitcoin (BTC) mixing platform, and according to OFAC, its primary function is to obscure transaction details, effectively concealing the flow of funds on the blockchain.
OFAC’s investigation has revealed that this mixer has been utilized by the infamous North Korean hacking group, Lazarus Group. Furthermore, it has been implicated in laundering funds obtained from the Harmony Horizon Bridge and Axie Infinity hacks. OFAC has now identified it as the “preferred mixing service” for the Lazarus Group, following the takedown of Blender.io. “Sinbad was used to launder a significant portion of the 0 million worth of virtual currency stolen on June 3, 2023, from customers of Atomic Wallet,” OFAC detailed.
“Mixing services that enable criminal actors, such as the Lazarus Group, to launder stolen assets will face serious consequences,” said Wally Adeyemo, the deputy secretary of the Treasury. “The Treasury Department and its U.S. government partners stand ready to deploy all tools at their disposal to prevent virtual currency mixers, like Sinbad, from facilitating illicit activities.”
This development comes in the wake of FinCEN’s recent update in late October, where it introduced new regulations requiring financial institutions to report transactions involving international cryptocurrency mixing services. At the time, Andrea Gacki, the director of FinCEN, and Adeyemo expressed their determination to combat illicit activities linked to digital currency mixing services.
Even before the proposed rules, the Treasury’s OFAC had been actively taking enforcement actions against mixers such as Blender and Tornado Cash. Simultaneously, OFAC had identified and flagged numerous sanctioned cryptocurrency addresses across various networks. The Treasury also warns that U.S. persons who “engage in certain transactions with the entity designated today may themselves be exposed to sanctions.”
What are your thoughts on this story? Let us know what you think in the comments section below.
Hackers Steal $4.4 Million From 25 Users of Lastpass Password Management App

Digital assets worth approximately .4 million were reportedly stolen from more than 80 addresses belonging to 25 users of the password management app Lastpass. Crypto theft investigator Zachxbt has urged crypto asset holders using the password manager to consider removing their keys and passphrases from the app.
More Than 80 Addresses Compromised
According to the online crypto theft investigator Zachxbt, approximately .4 million was stolen from more than 25 individuals using the password manager app Lastpass. The theft, which is said to have occurred on Oct.25, is suspected to be the work of a single threat actor. At the time of writing, more than 80 distinct addresses were compromised.
An analysis of the breach published on Chainabuse suggests that the theft may be “related to a larger case that dates back to at least December 2022.” As previously reported by Bitcoin.com News, the password management app’s cloud-based storage environment was breached in August 2022 but Lastpass only confirmed this on Dec. 22, 2022.
Following the revelation, Lastpass attempted to reassure worried users but this was largely met with scepticism.
Just on October 25, 2023 alone another ~.4M was drained from 25+ victims as a result of the LastPass hack.
Cannot stress this enough, if you believe you may have ever stored your seed phrase or keys in LastPass migrate your crypto assets immediately. pic.twitter.com/26HsxrlnCb
— ZachXBT (@zachxbt) October 27, 2023
Other Victims Urged to Share Transaction Hashes of the Thefts
Meanwhile, in a warning shared via the social media platform X (formerly Twitter), Zachxbt urged users of the password manager to remove their passphrases from the app.
“Just on October 25, 2023 alone another ~.4M was drained from 25+ victims as a result of the LastPass hack. Cannot stress this enough, if you believe you may have ever stored your seed phrase or keys in Lastpass migrate your crypto assets immediately,” Zachxbt cautioned.
The crypto investigator urged followers who may also be victims of the Lastpass hack to share the transactions hashes of the theft.
Reacting to Zachxbt’s post, some social media users appeared to blame the victims for having chosen to use the password management app in the first place. However, in response, the online investigator suggested that many people including unnamed high-profile people are using the app.
What are your thoughts on this story? Let us know what you think in the comments section below.
